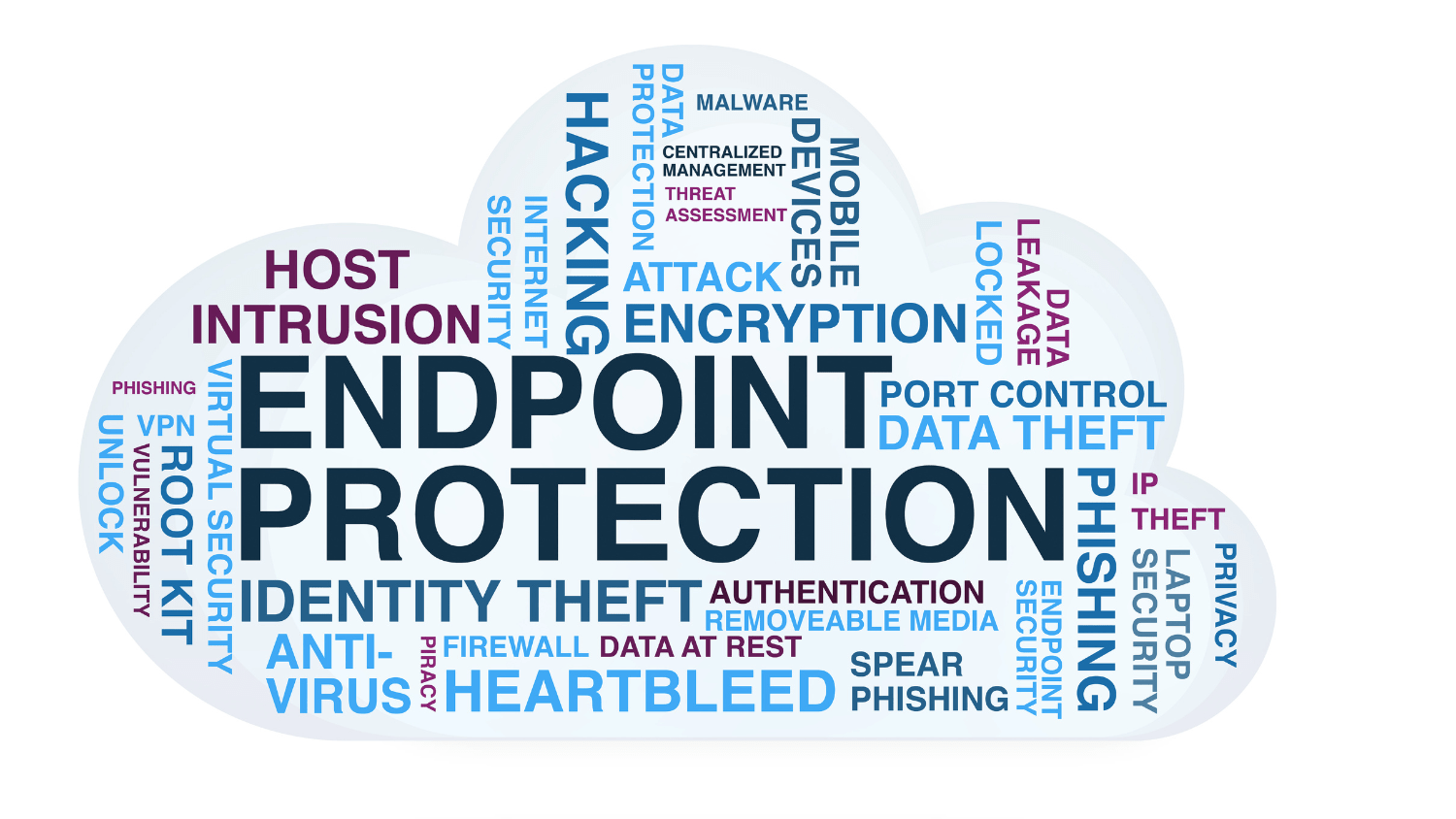
10 Essential Mobile Device Management Practices for Enhanced Security
Mobile devices have become indispensable tools for both personal and professional use. With the increasing reliance on smartphones and tablets for business operations, ensuring the security of these devices has become a top priority for organizations. Mobile device management (MDM) plays a critical role in safeguarding
Continue ReadingHow to Enable Guided Access on Android Devices Remotely
Smartphones play a crucial role in our daily lives, serving as indispensable tools for communication, productivity, entertainment, and more. However, for certain users, such as parents, educators, and businesses, managing and controlling access to smartphone features and applications is essential. This is where the concept of
Continue ReadingWhat is Endpoint Security? Role of MDM in Endpoint Security
The rapidly evolving landscape of cybersecurity challenges organizations to stay away from a multitude of threats targeting their digital assets. Endpoint security is a crucial aspect of cybersecurity, which focuses on securing individual devices connected to a network. This essay explores the concept of endpoint security,
Continue ReadingA Comprehensive Guide to Factory Resetting Android Devices
We all have encountered issues or some reason to fresh start our devices, whether you’re experiencing performance issues, software glitches, or simply want to wipe your device clean for a fresh start, performing a factory reset on your Android device can often be the solution. In
Continue ReadingBYOD, COPE, CYOD, and COBO – A Comprehensive Guide
The integration of mobile devices into the workplace has transitioned from being a mere choice to an absolute necessity. Since the inception of mobile devices, businesses have had to adapt to the demands of a modern, mobile-enabled workforce. This adaptation comes with the challenge of managing
Continue ReadingDeciphering the Differences: MDM, EMM, and UEM Explained
Devices like tablets, smartphones, laptops, handheld devices and rugged devices have enhanced productivity and improved communication, be it for the business or education industry. Managing these devices, applications, and data has become a paramount concern for organizations worldwide. Three key acronyms often surface in discussions surrounding
Continue Reading